TOP 5 CYBERSECURITY SOLUTIONS TO PROTECT YOUR BUSINESS IN 2024
Introduction
Cybercrime poses a huge threat to all kinds of businesses from large to small now that we rely on technology and the internet more than ever. Evidently, as technology advances, so do the tactics of cybercriminals, making it essential for organizations to stay two steps ahead. Criminals keep on finding new ways to break into systems and get access to vulnerable information. The fallout from cyber attacks can be devastating, ranging from financial losses to harming a company’s reputation. To stay safe, businesses need to understand these threats and take proactive measures to protect their systems and data. So, in this blog post, we will explore the top 5 cybersecurity solutions that businesses should adopt in 2024 to safeguard their sensitive information, maintain customer trust, and ensure the overall integrity of their operations.
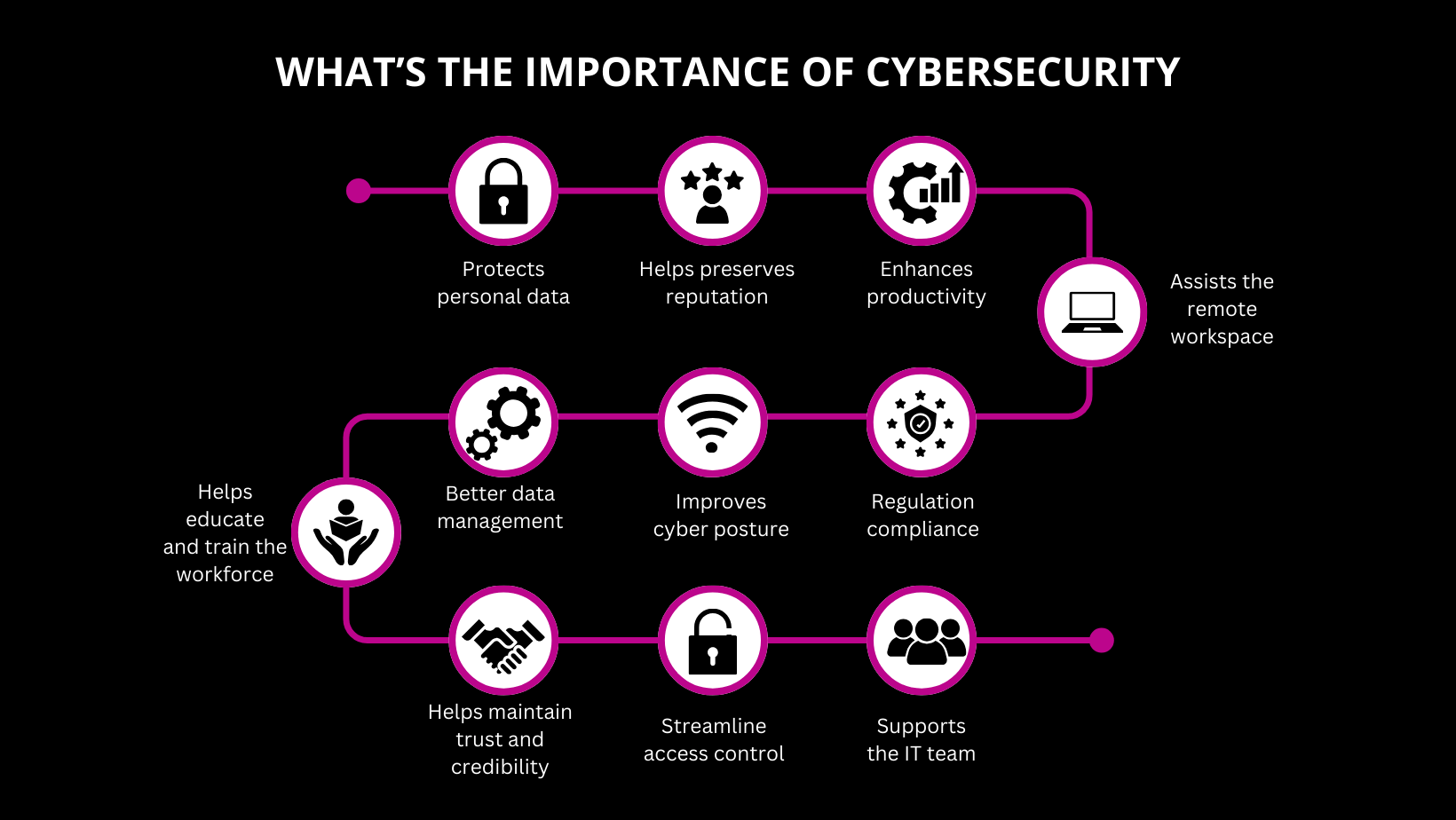
 Why is cybersecurity important for your business?
Why is cybersecurity important for your business?
Cybersecurity is crucial for businesses due to the rising frequency and sophistication of cyber threats. A successful cyber attack can result in financial losses, damage to reputation, and even legal consequences. So, with the increasing reliance on digital platforms, businesses are more vulnerable than ever to various cyber threats, including data breaches, ransomware attacks, and phishing scams. Additionally, implementing robust cybersecurity measures is not just a matter of protecting data; it is an essential aspect of maintaining the overall health and continuity of your business.
 Overview of common cyber threats
Overview of common cyber threats
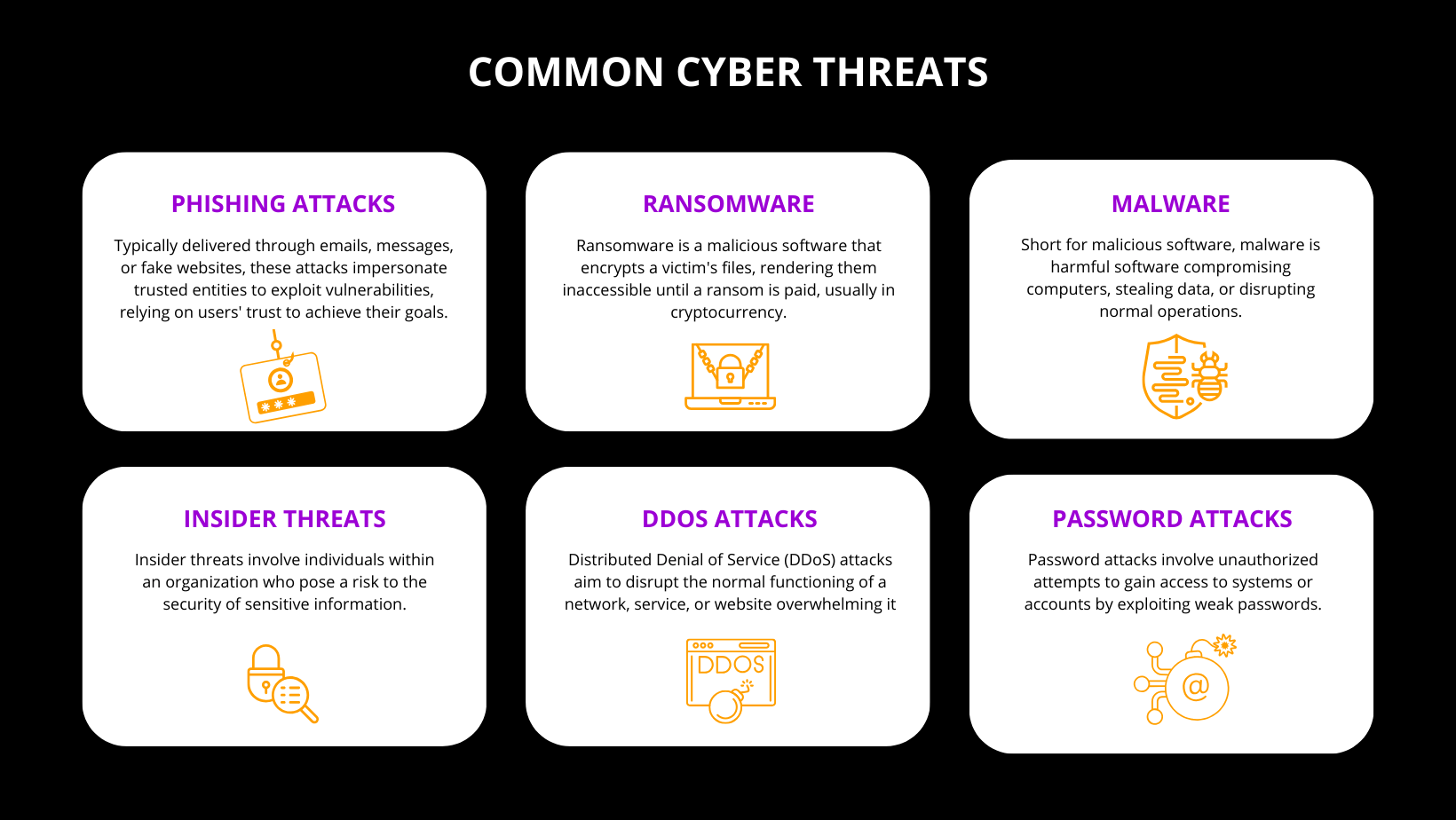
So, before delving into the top cybersecurity solutions, it’s important to understand the common cyber threats that businesses face. These threats include but are not limited to:
- Phishing attacks
- Ransomware
- Malware
- Insider threats
- DDoS attacks
- Password attacks
-
Phishing attacks
Phishing attacks involve deceptive tactics aimed at tricking individuals into divulging sensitive information such as usernames, passwords, or financial details. Typically delivered through emails, messages, or fake websites, these attacks impersonate trusted entities to exploit human vulnerabilities, relying on users’ trust to achieve their goals. Cybercriminals often employ social engineering techniques to manipulate recipients into clicking malicious links or downloading malicious attachments, compromising the security of individuals and organizations.
-
Ransomware
Ransomware is a malicious software that encrypts a victim’s files, rendering them inaccessible until a ransom is paid, usually in cryptocurrency. Cyber attackers employ various means to introduce ransomware, including phishing emails or exploiting vulnerabilities in software systems. This form of cyber threat poses a significant risk to businesses and individuals, as it can lead to data loss, financial losses, and operational disruptions.
-
Malware
Short for malicious software, malware encompasses a broad category of harmful software designed to compromise computer systems, steal data, or disrupt normal operations. Certainly, malware includes viruses, worms, Trojans, spyware, and other types of malicious code. Cybersecurity measures such as antivirus software and regular system updates are crucial for protecting against malware threats.
-
Insider threats
Insider threats involve individuals within an organization who pose a risk to the security of sensitive information. This threat can be unintentional, such as employees inadvertently exposing confidential data, or intentional, with malicious insiders deliberately compromising systems. Organizations must implement strict access controls, monitor user activities, and provide cybersecurity training to mitigate the risks associated with insider threats.
-
DDoS attacks
Distributed Denial of Service (DDoS) attacks aim to disrupt the normal functioning of a network, service, or website by overwhelming it with a flood of traffic. Perpetrators use multiple compromised computers or devices to launch the attack, rendering the targeted system inaccessible to legitimate users. DDoS attacks can lead to service downtime, financial losses, and reputational damage, emphasizing the importance of robust cybersecurity measures, including traffic filtering and mitigation strategies.
-
Password attacks
Password attacks involve unauthorized attempts to gain access to systems or accounts by exploiting weak or compromised passwords. Common techniques include brute force attacks, where attackers systematically try numerous combinations, and credential stuffing, using previously leaked or stolen passwords. Also, to enhance cybersecurity, individuals and organizations should enforce strong password policies, employ multi-factor authentication, and regularly update passwords.
Now, let’s explore the top 5 practices for cybersecurity that can help businesses stay resilient in the face of these threats.
 Top 5 Cybersecurity Solutions:
Top 5 Cybersecurity Solutions:
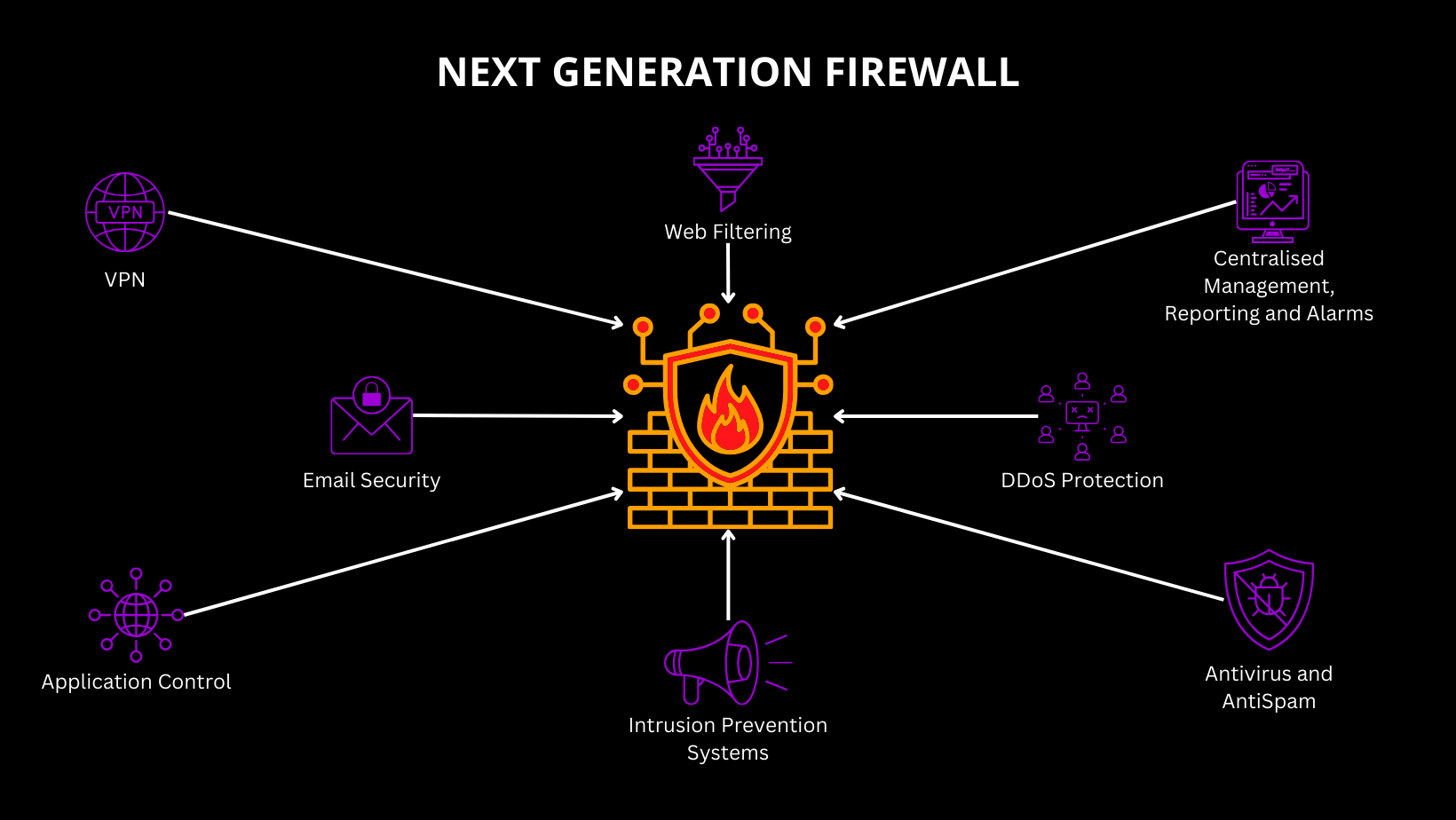
Next-Generation Firewalls
Next-generation firewalls (NGFWs) go beyond traditional firewalls by providing advanced threat detection and prevention capabilities. Basically, they analyze network traffic in real-time, identifying and blocking malicious activity before it can compromise the system. In 2024, businesses should invest in NGFWs with features like intrusion prevention, application control, and advanced malware detection to fortify their network defenses.
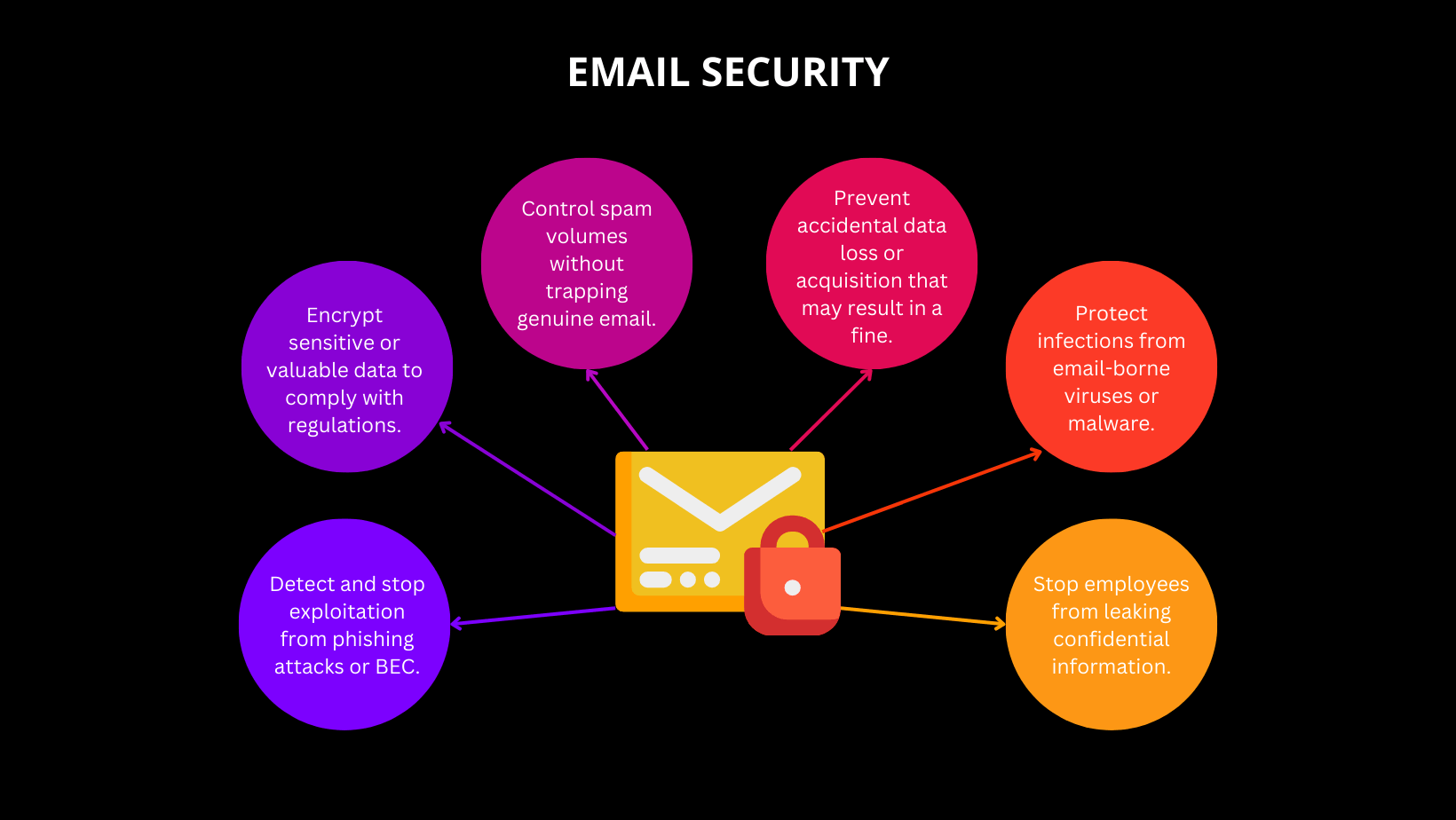
 Email Security
Email Security
Later, email remains a primary vector for cyber attacks, with phishing being a prevalent threat. Implementing robust email security solutions involves deploying advanced spam filters, email encryption, and user training programs to educate employees on recognizing and avoiding phishing attempts. In 2024, businesses should prioritize email security to mitigate the risks associated with malicious attachments and deceptive email content.
 Cloud Backup
Cloud Backup
Certainly, the increasing adoption of cloud services necessitates a focus on securing cloud-based data. Cloud backup solutions play a crucial role in ensuring data resilience and recovery in the event of a cyber incident or data loss. Businesses should implement reliable cloud backup strategies to safeguard their critical information, providing an added layer of protection against ransomware attacks and accidental data deletion.
Anti-Malware and Endpoint Protection
Protecting endpoints, including computers, laptops, and mobile devices, is paramount in the current threat landscape. Businesses should deploy advanced anti-malware solutions that offer real-time threat detection, behavioral analysis, and endpoint protection. Generally, endpoint security measures help prevent malware infections and secure devices that connect to the corporate network, reducing the risk of unauthorized access and data breaches.
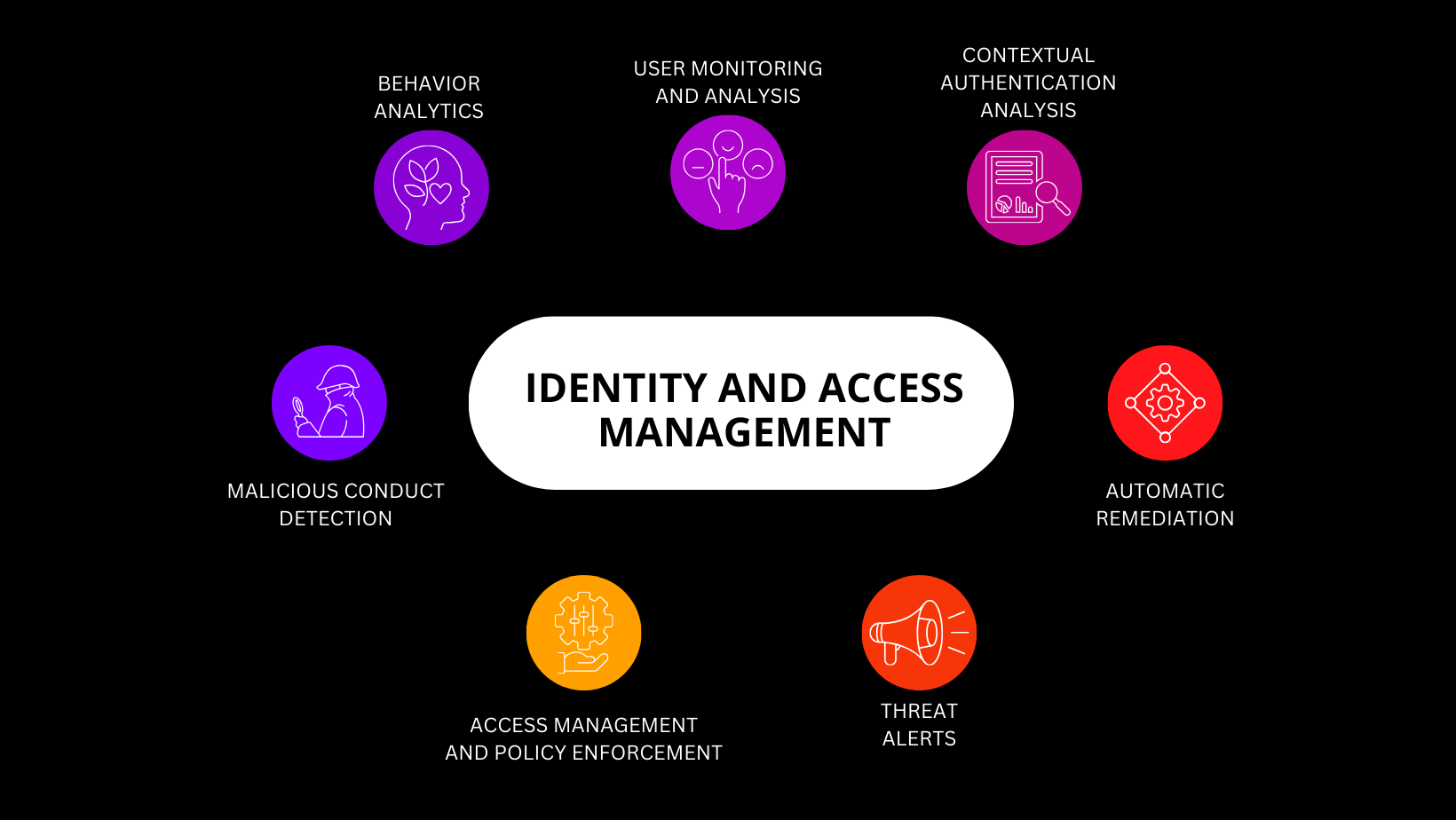
Identity and Access Management
Furthermore, identity and access management (IAM) is essential for controlling and monitoring user access to sensitive systems and data. In 2024, businesses should implement IAM solutions that include multi-factor authentication, role-based access controls, and continuous monitoring of user activities. Besides, strengthening identity management ensures that only authorized personnel have access to critical resources, reducing the risk of unauthorized access and insider threats.
 Conclusion
Conclusion
As businesses navigate cyber threats in 2024, prioritizing cybersecurity is not just a choice; it’s a necessity. Implementing a multi-layered approach that includes next-generation firewalls, email security, cloud backup, anti-malware and endpoint protection. Consequently, together with identity and access management this all is crucial for creating a robust defense against evolving cyber threats. Besides, by adopting these top cybersecurity solutions, businesses can safeguard their operations, protect sensitive information, and fortify their resilience.
Finally, protecting your business from cyberthreats in 2024 will undoubtedly be a challenging task. Contact ProArea today to consult on the matter.